Hacking: Hacking for Beginners: Computer Virus, Cracking, Malware, IT Security (Cyber Crime, Computer Hacking, How to Hack, Hacker, Computer Crime, Network Security, Software Security): Connor, Joseph: 9781539860723: Amazon.com: Books
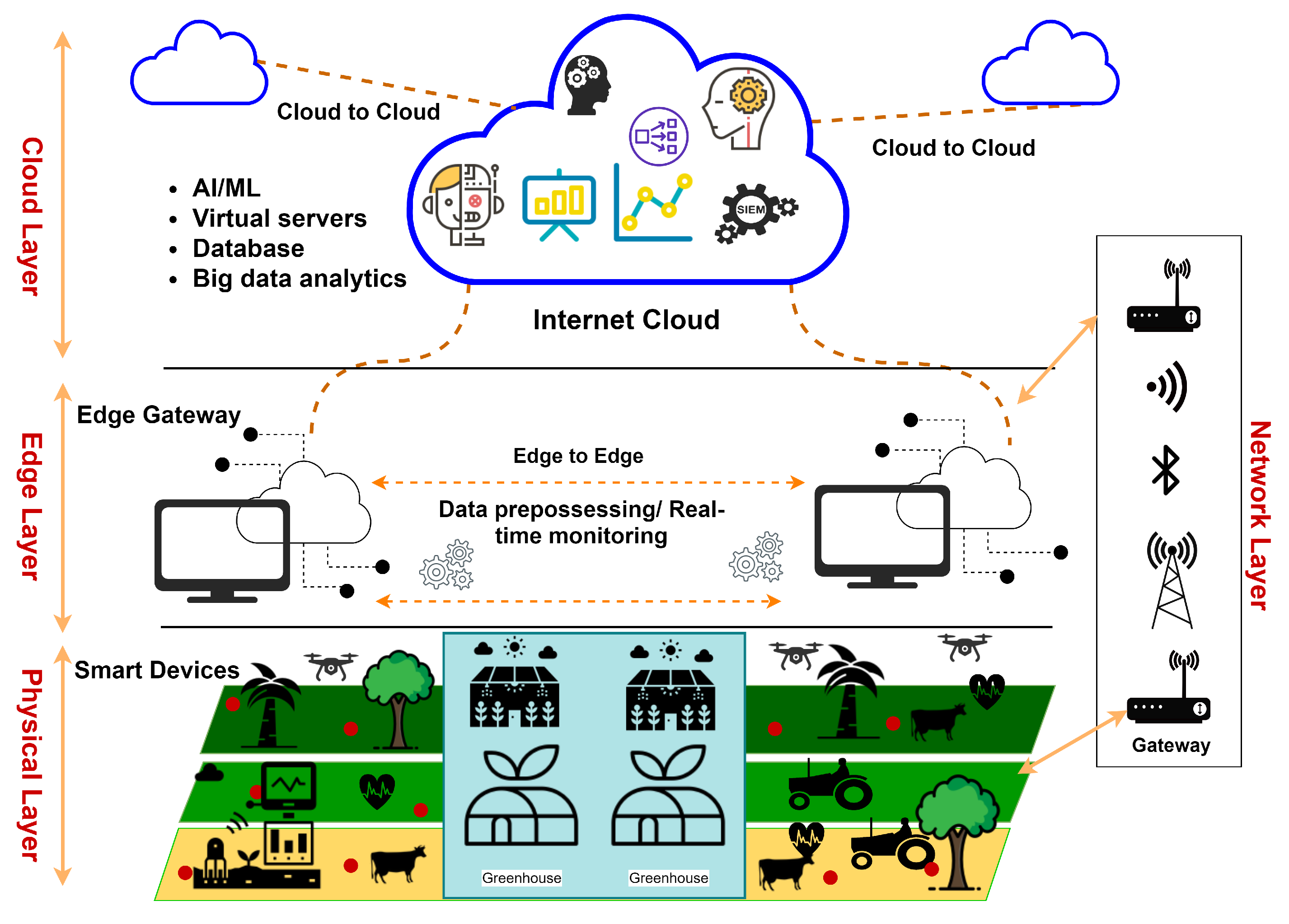
Applied Sciences | Free Full-Text | A Review on Security of Smart Farming and Precision Agriculture: Security Aspects, Attacks, Threats and Countermeasures
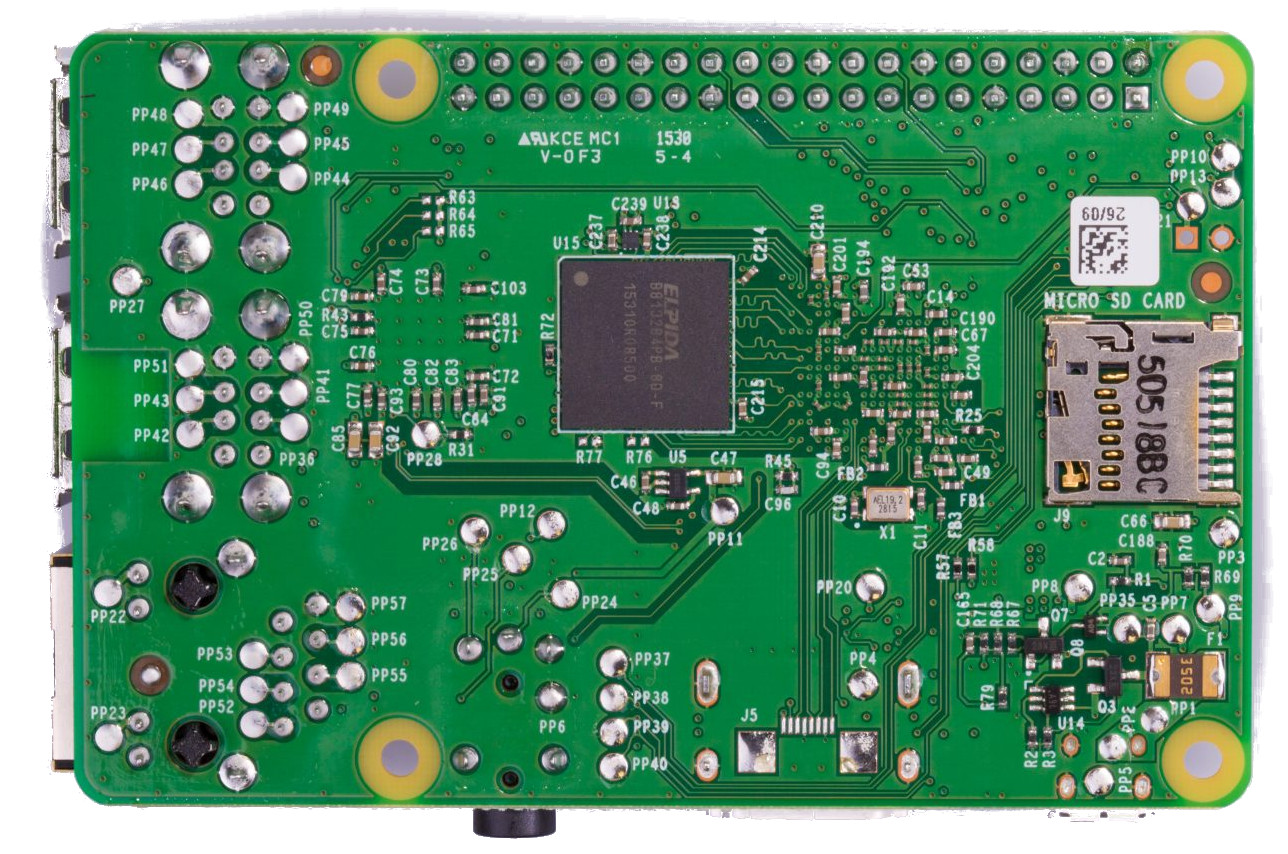
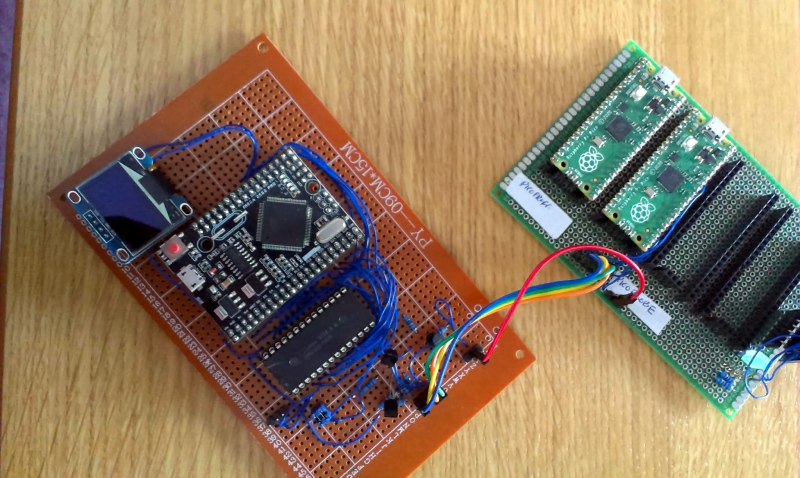
Getting Started with Raspberry Pi 2 Model B v1.1 – vnc setup display 0 and 1 – how to wire setup 12v relay card | dwaves.de

Attracting Hackers - Honeypots For Windows (Books For Professionals by Professionals) PDF | PDF | Malware | Information Age

Installing Kali Linux on a Raspberry Pi and Connecting to it Remotely – CYBER ARMS – Computer Security
![PDF] Drone Hacking with Raspberry-Pi 3 and WiFi Pineapple: Security and Privacy Threats for the Internet-of-Things | Semantic Scholar PDF] Drone Hacking with Raspberry-Pi 3 and WiFi Pineapple: Security and Privacy Threats for the Internet-of-Things | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a84bd8f41d2225cbf8224963b02d926c196a0b60/5-Figure11-1.png)
PDF] Drone Hacking with Raspberry-Pi 3 and WiFi Pineapple: Security and Privacy Threats for the Internet-of-Things | Semantic Scholar

Free Online Course: Communications and High-Speed Signals with Raspberry Pi from Coursera | Class Central

Electronics | Free Full-Text | SUKRY: Suricata IDS with Enhanced kNN Algorithm on Raspberry Pi for Classifying IoT Botnet Attacks


.jpg)